The threat of cyber-attacks looms larger than ever, with phishing schemes becoming increasingly sophisticated and automated. Organizations and consumers must stay vigilant and informed to protect themselves from these malicious tactics. With the continuous advancement of technology, cybercriminals are constantly refining their strategies, making it crucial for everyone to understand the risks and take proactive steps towards securing their online activities.
Understanding Phishing Attacks
Phishing attacks are fraudulent attempts to obtain sensitive information such as usernames, passwords, and credit card details by disguising as a trustworthy entity in electronic communications. These attacks often involve emails, text messages, or websites that appear legitimate but are designed to steal personal information. Once you click, these links can steal your personal information like passwords, credit card details, or even login credentials for business accounts.
The Rise of Automated Phishing
Phishing attacks have evolved with technology, becoming more automated and harder to detect. Cybercriminals now use mass emails with personalized content, making them appear legitimate. This automation increases the risk of falling victim to these scams.
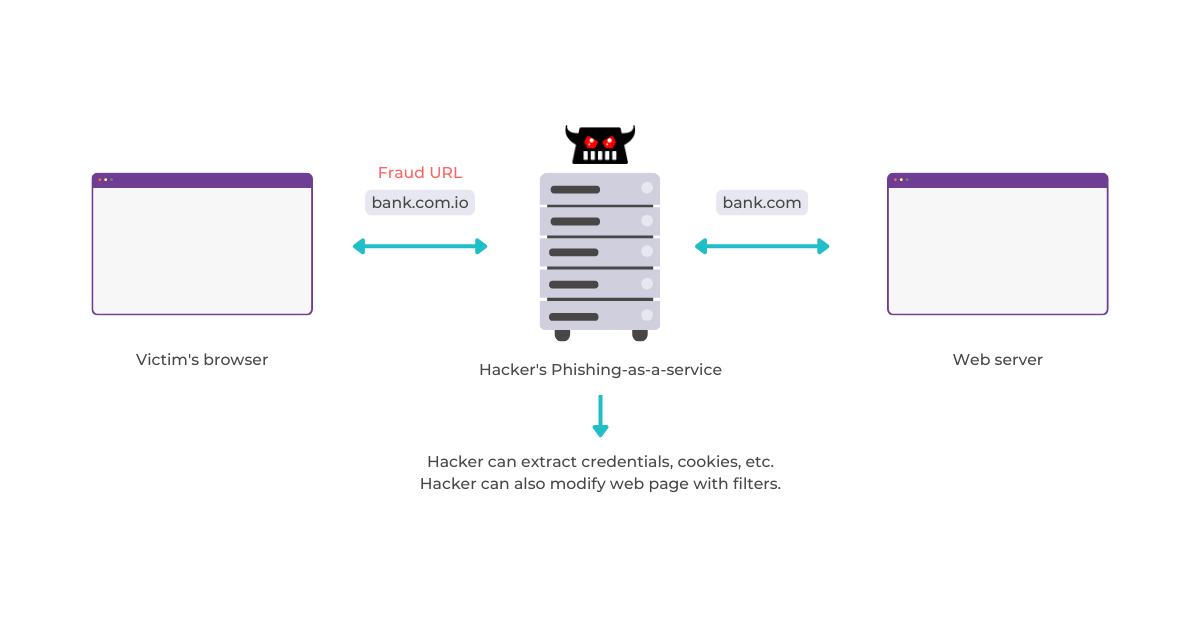
Automated phishing attacks, made possible by tools like Evilginx3, are becoming increasingly common. These tools allow attackers to create fake websites quickly and easily, making it even harder to distinguish them from the real thing.
Here’s how Evilginx3 makes phishing easier for attackers:
Pre-built Templates: Evilginx3 comes with pre-built templates for popular websites, allowing attackers to set up a convincing fake website in minutes.
Man-in-the-Middle Scheme: Evilginx3 acts as a middleman between your browser and the fake website. It intercepts your communication with the fake website, stealing your login credentials or other sensitive information you enter.
Bypassing Security Measures: Evilginx3 can bypass some security measures, making it even harder to detect a phishing attempt.
The Dangers of Evilginx3:
Examples of Phishing Attacks:
- Email Phishing: An attacker sends an email that appears to be from a reputable source, such as a bank or a well-known company. The email contains a link that directs the recipient to a fake website, where they are prompted to enter their personal information.
- Spear Phishing: A more targeted form of phishing, where the attacker customizes their message to a specific individual, often using personal information to make the email more convincing.
- Smishing and Vishing: Smishing involves sending fraudulent text messages, while vishing involves making phone calls to trick individuals into providing their personal information.
The Impact of Phishing Attacks
The consequences of a successful phishing attack can be devastating. Here’s what’s at stake:
- Financial Loss: Hackers can steal money directly from your accounts or use stolen credit card information for fraudulent purchases.
- Data Breaches: Phishing attacks can be used to steal your sensitive data, leading to hefty fines and reputational damage.
- Disruptions: Phishing attacks can disrupt operations by infecting devices with malware, hindering productivity and causing system downtime.
How to Mitigate Phishing Attacks
To effectively mitigate the risks posed by automated phishing attacks, organizations can implement several proactive measures:
- Stay Informed: Educate yourself about common phishing tactics so you can recognize suspicious emails or messages.
- Enable Multi-Factor Authentication (MFA): MFA adds an extra layer of security by requiring a second verification step beyond a password for access. Mobile app shielding can complement MFA by protecting the entire app ecosystem, ensuring that even if one factor is compromised, the app remains secure.
- Beware of Urgent Requests: Phishing attempts often try to create a sense of urgency to pressure you into acting quickly without thinking critically. If an email or message demands immediate action, proceed with caution.
- Only Feed Trusted Sites: Only enter personal information on websites you absolutely trust. Double-check the URL – a single typo could be a red flag. Look for the padlock symbol in your browser’s address bar to indicate a secure connection (HTTPS).
A Multi-Layered Defense Against Phishing
V-Key offers a multi-layered defense against phishing, empowering businesses and individuals to stop these attacks and protect valuable data including V-OS Web Shield and App Shield.
V-OS Web Shield
V-OS Web Shield blocks access to fake websites designed by attackers, preventing your login credentials or other sensitive information from being compromised. It utilizes digital signatures to verify the website’s authenticity.
How V-OS Web Shield Works
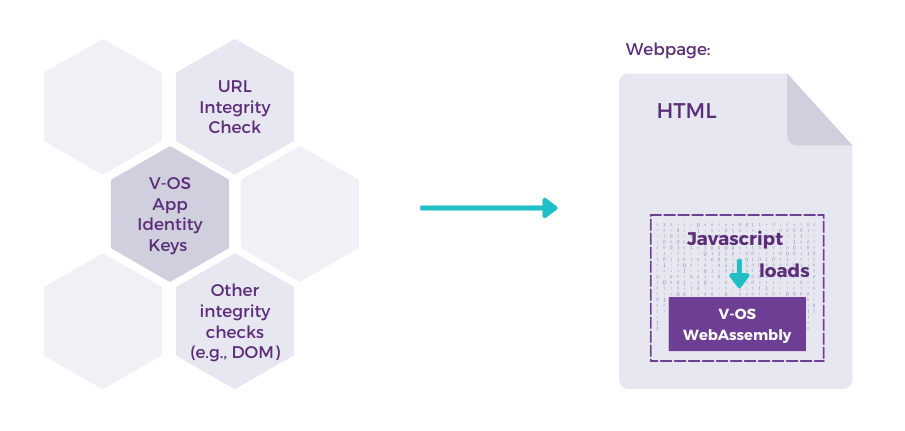
V-Key’s V-OS WebAssembly (WASM) is delivered within the web site via a JavaScript call (on the website, executed by the end-user’s web browser when the user browses to the website), and verified with a back-end call to ensure that only the protected user can connect to the protected website.
V-OS App Shield bolsters your defenses by safeguarding your mobile applications. It encrypts sensitive data and thwarts malware attempts to infiltrate your device. Even if you click a phishing link, this extra layer of protection makes it significantly harder for attackers to steal your information.
An additional layer of security that goes beyond passwords. It generates unique digital signatures or time-based codes for logins, making it even harder for attackers to steal your credentials even if they bypass your password.
Your Trusted Phishing Defense
V-Key empowers businesses of all sizes to combat phishing and security breaches. Here’s how V-Key helps businesses reel in these deceptive attacks:
- Reduced Risk of Data Breaches: V-Key’s solutions act as a first line of defense in preventing hackers from stealing valuable customer data or financial records.
- Enhanced Brand Reputation: A phishing attack that compromises customer data can undermine a company’s reputation. V-Key’s solutions safeguard businesses from this risk, helping to maintain a positive brand image and build customer confidence.
- Regulatory Compliance: Many regulations mandate businesses to protect customer data. V-Key’s solutions simplify compliance with these regulations
Embracing a Proactive Defense
By remaining vigilant and taking proactive steps to protect yourself online, you can reduce the risk of falling victim to phishing attacks. Additionally, implementing robust security strategies , you can create a more secure environment.