V-OS Protection against Android Plugin malware
There has been a recent surge in Android malware abusing Android Plugin Frameworks for malicious behavior. DroidPlugin, Parallel Space and VirtualApp are several plugin frameworks that have been abused by malware in recent months to spread Android malware.
Android Plugin Frameworks Overview
Android Plugin Frameworks are a way to run multiple instances of an application on the same device. The original use case is to enable users to sign into multiple accounts of the same service, e.g. social media services such as Facebook/Instagram/Twitter. This allows the user to, for example, manage a business and personal social media account simultaneously on the same device without having to sign out/sign in.
Technology
Android Plugin Frameworks work by creating an application level virtualization framework that allows a host mobile app to dynamically load and launch another app (plugin) without actually installing it on the device. To do so, it hooks several critical Android APIs that are involved in:
- loading/launching Android APK files without installation
- app component lifecycle management
- inter-plugin communication
- plugin management.
In doing so, it is able to modify the flow of the app during runtime, and change its behavior.
Source: Anti-Plugin: Don’t Let Your Apps Play As An Android Plugin by Tongbo Luo et al
Malware Abuse
While Android Plugin technology has several legitimate, benign use cases, it has also been abused by malware developers, who have used it to update/install new malware without root access, evade static detection, and phish on authenticated apps without repackaging. As the plugin app runs within the host app, and the host app hooks vital Android APIs, the host app is by and large transparent to the plugin app. However, the fact that the host app is hooking the Android APIs without the plugin’s knowledge makes this a critical attack vector.
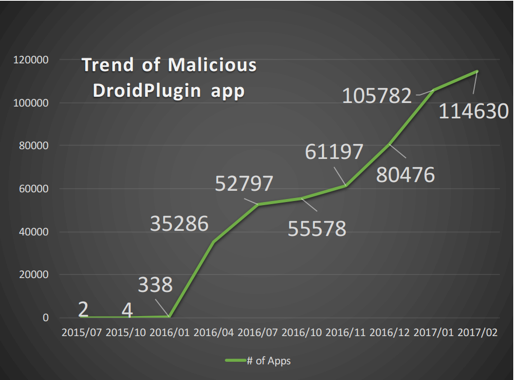
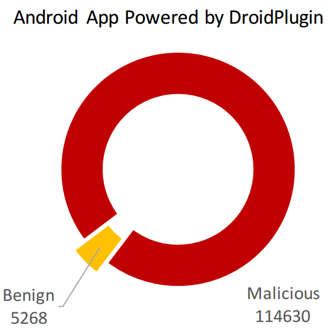
DroidPlugin in particular is an open source Android Plugin Framework SDK that allows developers to quickly create apps leveraging on Plugin technology. As shown in the charts below, it has been overwhelmingly used for malicious intents. VirtualApp is a similar Android Plugin Framework that malware authors have abused.
Source: Anti-Plugin: Don’t Let Your Apps Play As An Android Plugin by Tongbo Luo et al
Risks of Plugin malware
If Plugin framework malware were allowed to install trusted apps as plugins, the risks are significant. Consider a trusted banking app that is installed in a host plugin malware as a plugin. The malware could potentially intercept generated OTP images. It could also phish on user credentials during the login process, since it controls key app component management APIs.
Protections within the V-OS Trust Platform
The use and abuse of Android Plugin Frameworks are a relatively new occurrence, and the V-OS Trust Platform does not have any specific checks for it. However, plugins leverage hooking mechanisms to operate, which are already detected and blocked by V-OS App Protection. In fact, all known Plugin Frameworks currently hook on app component lifecycle management APIs, specifically ones pertaining to the creation of Activities.
The V-OS Trust Platform has a wide array of anti-hooking mechanisms to protect against reverse engineering and active attacks. Since Android Plugin Frameworks leverage on hooking to operate, the V-OS Trust Platform therefore already works out of the box to detect them. As a result, when an app leveraging on V-OS App Protection is launched as a plugin in a host app, V-OS App Protection will detect the plugin and block access to the cryptographic keys and identity. Our Security Research team has already tested a wide range of apps utilizing Android Plugin Frameworks, and verified that V-OS App Protection successfully detected when it is run as a plugin in all of them, and prevented malware attacks. The V-OS Trust Platform therefore remains secure in the presence of a Plugin Framework. What this means is that existing V-Key customers are already safe from Plugin malware.
Conclusion
Security is critical in V-Key’s entire product line, and our Security Research team continuously monitors the horizon for new and emerging threats, developing holistic mechanisms that protect against them. In addition, V-OS App Protection was also designed from the start to decouple its security from that of the untrusted underlying OS. This naturally extends to an untrusted Plugin Framework. The result is that V-Key integrates state of the art protection mechanisms that keeps our customers safe from even such zero-day attacks.