13 July 2020 Singapore, Singapore Crunchfish AB (“Crunchfish”) announces today that the company has entered into a Marketing & Technical Partnership Agreement with V-Key Pte Ltd (“V-Key”) regarding identifying and developing joint offerings of each party’s software product in relation to Crunchfish’s… Read More
Resources

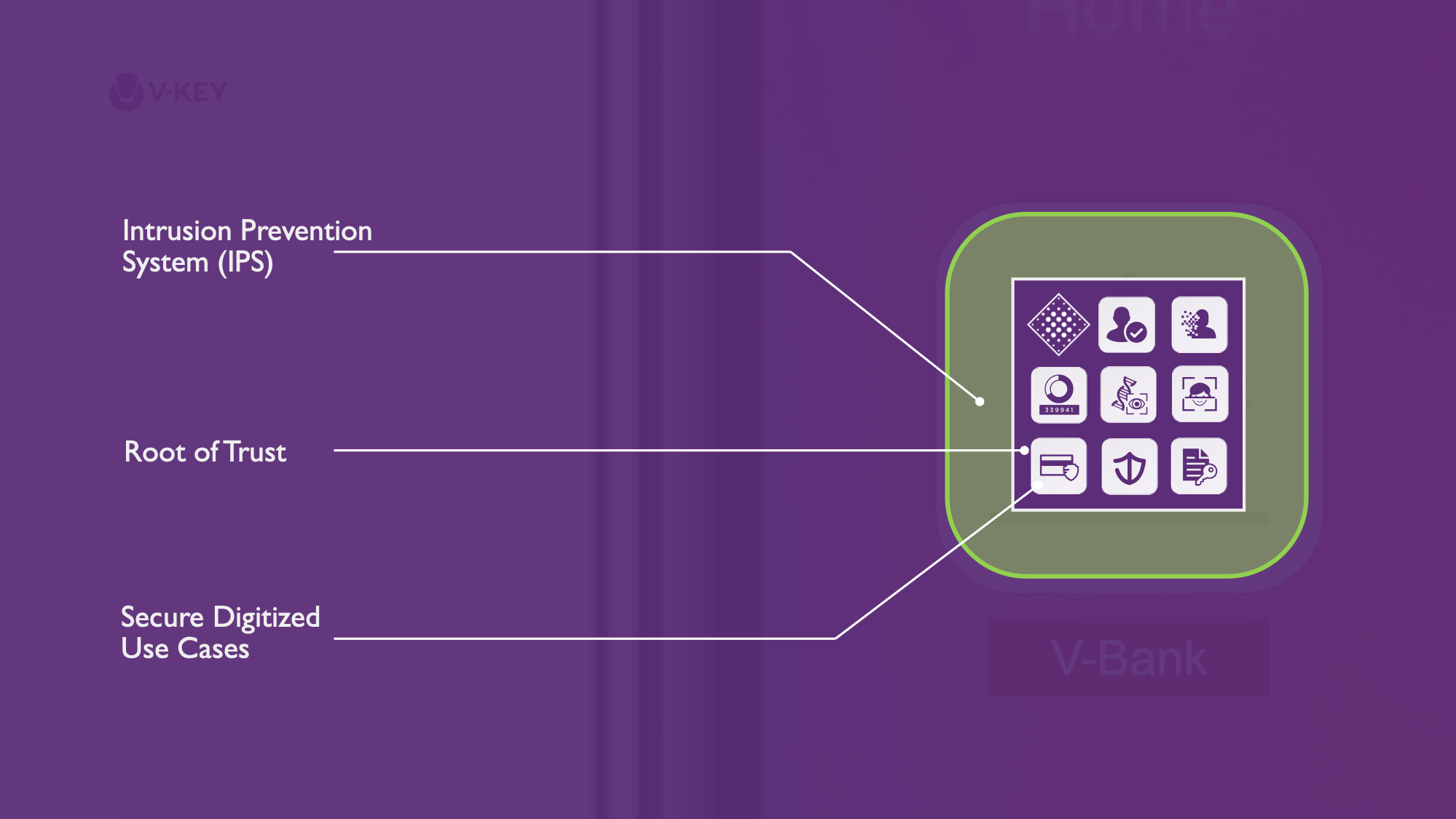
World’s First Virtual Secure Element V-OS obtains Common Criteria EAL3+ on iOS and Android.
6 July 2020 SINGAPORE, SINGAPORE V-Key announced that V-OS, V-Key’s core patented technology, is the world’s first virtual secure element to receive a Common Criteria Evaluation Assurance Level (EAL) rating of 3+, derived from the U.S. Government’s Protection Profile for General Purpose… Read More
How to survive a hacking attack?
A data breach can be devastating – lost customer trust, financial penalties, and reputational damage. This white paper equips you with 10 essential questions to evaluate your mobile security system and ensure your app survives a hacking attempt. Uncover your vulnerabilities… Read More

TONIK chooses V-Key as the Mobile Security Partner for its Digital Bank in the Philippines
6 May 2020 SINGAPORE, SINGAPORE V-Key’s V-OS App Protection on V-OS Cloud to secure the first pure-play Digital Bank in the Philippines. V-Key announced today that it has been chosen to be the mobile security partner of TONIK digital bank, to provide a… Read More
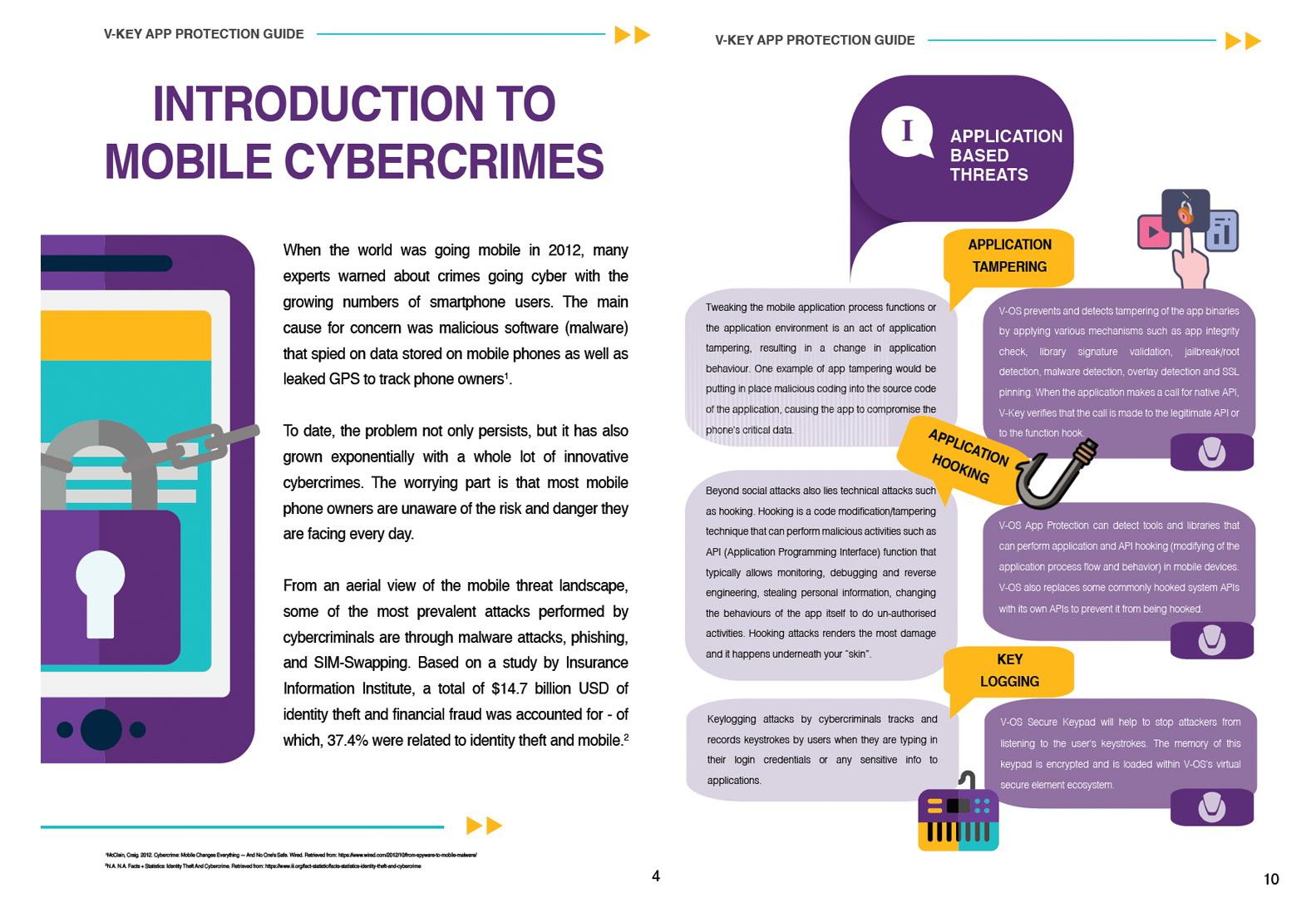
App Protection Guide
Today’s smartphones hold a wealth of sensitive data – banking information, personal documents, and more. Cybercriminals are constantly developing new methods to exploit these vulnerabilities, putting your privacy and security at risk. This white paper will equip you with the… Read More
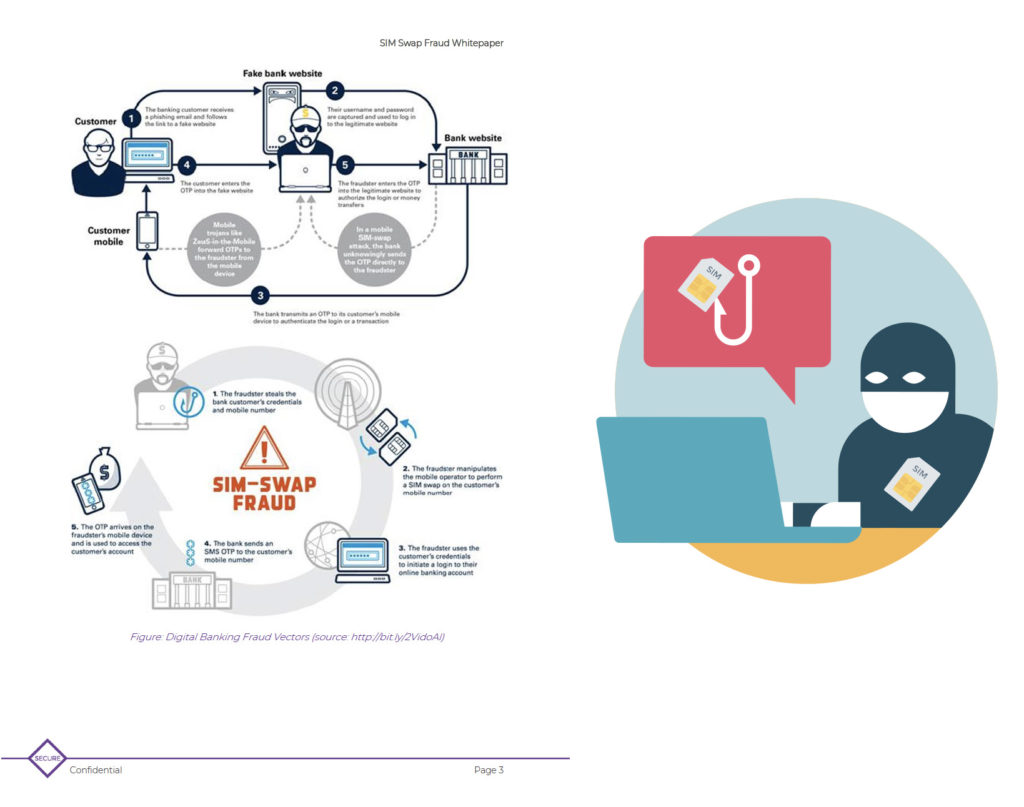
Sim Swap Fraud
What is SIM swap scam SIM swap scam (also known as SIM jacking, SIM splitting, or Port-Out scam) is a type of account takeover fraud that exploits the weakness in conventional methods of two-factor authentication/verification. More often than not, this attack… Read More
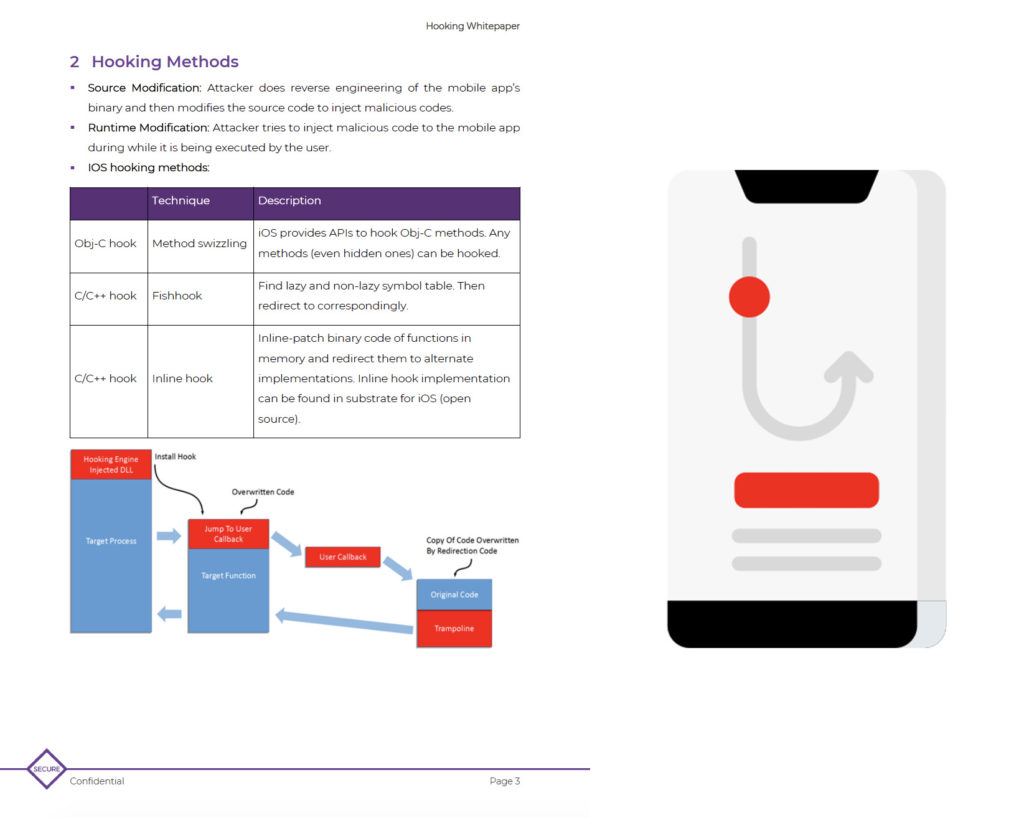
Application Hooking
What is Hooking Hooking is a term for a range of code modification/tampering techniques that are used to change the behaviour of the original code running sequence by inserting instructions into the code segment at runtime. Find out from this whitepaper why… Read More

V-Key Collaborates With SGTech and IMDA For COVID-19 Support
26 March 2020 SINGAPORE, SINGAPORE COVID-19 has pushed the majority of the world’s workforce to exercise the largest work-from-home movement. Local deep-tech SME, V-Key, participates in an initiative led by SGTech and jointly with IMDA to provide secure 2FA Cloud authentication solutions. The… Read More
V-Key Business Continuity Plan Commitment
March 25, 2020 With COVID-19 on the minds of many, we want to take a moment to personally update you on the steps we are taking at V-Key to ensure the continuity of our business and support functions of our customers. V-Key is committed to ensuring that we are… Read More
Is the detection of jailbroken/rooted phone sufficient against threats?
Is the detection of jailbroken/rooted phone sufficient against threats? It is widely known that performing jailbreaking/rooting opens the mobile device to security vulnerabilities. It often leaves a gap for malware to gain elevated permissions on a device. This elevated access allows… Read More

